
Data Forensics
[ Overview ]
Data is ever harder to disconnect from and often shows the profile of the user.
[ Data Interrogation ]
Using the latest computer forensic technology to interrogate:
-
Mobile phones (Smart and non smart)
-
Laptop computers
-
Desktop computers
-
Local storage devices HDD, SSD, flash drives, SD & Micro SD
-
Server data banks
-
Remote storage, inc: cloud data
We are currently running:
-
Forensic Tool Kit 8.1
-
Guidance Software - En Case Forensic
-
Oxygen Forensics - Detective
Other applications are available.
We can use a mix of programs to cross validate the interrogated data.
We offer a back at base examination, or a field service.
[ Data Mirroring Service ]
To capture the data we also offer "data mirroring service" where we attend site and copy data from the target drive to source drives. This a bit for bit mirror where data blockers are used to protect the original evidence.
[ Spyware investigation ]
Using our data forensic suite we can investigate for the presence of hidden covert spyware on any device. There is currently a popular range of spyware apps that uploads every keystroke/image/voice call to a remote server where all data is captured and is recoverable by the spy. We can detect and counter this issue.
[ Penetration testing and data hardening ]
Pen testing can be undertaken probing for weakness, not only password evaluation but infrastructure compliance. Procedures need constant review as do electronic updates. We find the simple mistakes lead to the biggest failures.
In a recent TSCM sweep of a Government Finance Department in the Middle East we gained full access to the network servers and client details through a recent fitment of a new replacement access point straight from the box. This failing lead to an internal investigation and data hardening process.
[ Network Analytical interception ]
Tactical HTTPS - SSL Lan Intercepting System - Cybereye. This network analyser is sited within your own network between the main switch and router. It monitors all inbound and outbound traffic filing and storing for live online and offline interrogation at a forensic level. This is a key element in identifying hacking attempts and any data movements/extractions.
[ Triage service ]
We attend your office and capture the most fruitful data in the early stages of an investigation. Data is very difficult to destroy / delete / erase and we can capture the data that has recently been erased "placed in the bin then deleted" which is often the incriminating informative intelligence.
[ Data Catchers Video & keyboard - hardware on PC's ]
Where a local capture solution is required we can offer a video screen capture and a key stroke capture. The screen capture device stores an image every second as JPEG's. The key stroke device stores the ASCI key board activity as raw text in the local 4Gb storage. This is excellent for passwords, emails and documents, with wifi connection options.
These can be external slot in devices or the modules can be integrated into your range of keyboards and/or monitors with wifi downloadable connectivity.
These services often are complimented by our Technical Surveillance Counter Measure activities


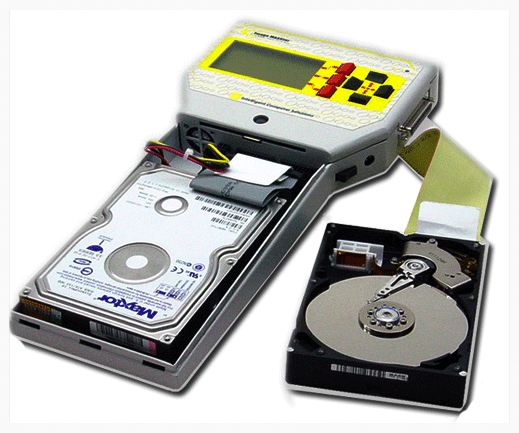
This device is a hard drive duplicator. A bit for bit mirror of the original HDD allowing live investigation back at base.
